This newsletter brings all the previous newsletters together in one place – Identity in a nutshell, so to speak. I think it appropriate to summarize the basics of Identity before, in following newsletters, going more in-depth, critiquing different approaches, and suggesting what the future will look like.
So here it is – Identity as well as I know it; based on my experience and documented in my previous eight newsletters. The process of summarizing these eight newsletters suggested some revisions and these have been made to this summary edition.
Identity is important for Society
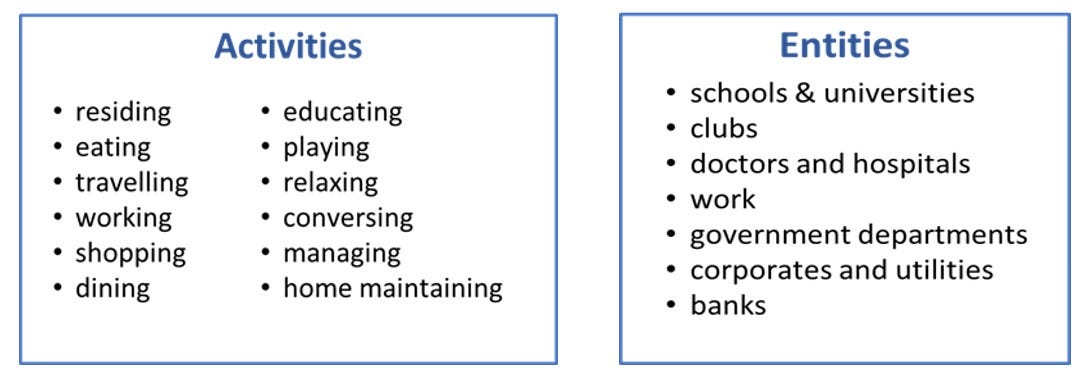
The starting point is Identity’s importance for society. Consider the list of activities and entities below.
Clearly, a number of the activities involve identifying ourselves, and many of our relationships with the entities shown are based on identity. We identify ourselves regularly in many situations that require security, and we want such services to be easy-to-use and convenient. Identity is not a nice-to-have – it is part of the very fabric of our society and our legal system. Identity is important!
Identity-based Transactions
I use the term transaction in an everyday manner “to carry on or conduct business… to a conclusion”. That is, a transaction is a sequence of actions with a specific form and time period. Of course, not all transactions involve identity as shown in the picture below.
Transactions split into anonymous transactions and identity-based transactions. Examples of anonymous transactions are buying a ticket for a movie or buying an ice cream. At no time are you identified and you are anonymous (this is not to say that you cannot be traced, but that is another story…).
These newsletters are all about the identity-based transactions (in the red circle above). In these transactions, the person’s identity is important. These transactions are for a specific individual.
I differentiate identity-based transactions into named and nameless. Most transactions are named, meaning that the recipient of the information wants to know who you are – they want to know your name. In the alternative, nameless transactions, the recipient does not know your name. This is how a covid-passport should operate – the recipient knows you are covid-free but does not know your name – you are nameless.
Identity Processes
There are two basic identity processes that occur within identity-based transactions.
The first process, identification and authentication, is obvious and very important. An identity-based transaction needs an identification and authentication process appropriate to the risk of the transaction. Buying a house needs more security than taking a book out of the library. Identification and authentication is the hard, stressful bit, hence the red colour.
And every transaction has a purpose beyond identification and authentication, and this purpose is achieved either through the use of some personal data or the sharing of personal data. An example of use of data is checking that a person has the required permission for entry, while an example of data sharing is opening a new account. This is more about growth, hence the green colour.
Both processes are important. Without appropriate identification and authentication, fraud can occur. Without data use or data sharing the transaction cannot achieve its purpose.
The ‘Real Context’: Parties and Environments
I write ‘real context’, because the number of parties and the environment are where Identity ‘really happens’.
The diagram above shows the inescapable two dimensions of Identity: the parties who are involved, and the place where they transact. They are inescapable because this is how our world is organized.
For parties, there are 2-party and 3-party identity-based transactions. 2-party transactions are simply a person and an organization, while 3-party transactions involve a person, an organization that knows the person, and an organization that does not know the person. 3-party is the difficult situation of proving to someone, who has never met you, that you are who you claim to be.
The places are the obvious ones: the physical environment, communicating on the telephone, and the on-line world. While these are obvious, each environment has quite different communication possibilities and, when combined with both 2-party and 3-party transactions, there is a lot of variety and complexity.
So, parties and place are the real context of Identity, and it is not a simple context.
Identity Performance
Given the context above, how well does Identity do? Well, it’s not great. In the diagram below, performance is shown using traffic light colours: green = good, orange = ok, red = bad.
The judgements above are mine. I find that the only redeeming feature of identity is the availability of 2-party solutions. If I think about ease of use for 2-party transactions, I find cards in a physical environment mostly good, answering 20 questions to identify myself on the telephone as painful, and the online experience as being excruciating, with check codes and the like varying service by service and, it seems, by the time of the day! 3-party ease of use is worse, and security and cost just do not look good anywhere.
Identity is not easy to use, Identity is not secure, and Identity is not cheap. This is not good news.
Current Status of Markets and Technologies
So what is behind and in front of all this poor performance?
Well, we have established market segments of Identity (the top half of the above diagram), but these are somewhat eclectic having evolved in a series of near accidents. For example, Know Your Customer only exists because of Anti-Money Laundering / Countering the Financing of Terrorism legislation. These segments do not share common origins or common strengths, but do share common problems.
Notwithstanding the eclectic nature of the market, there are several enabling and developing Identity technologies that have strengths and potentials (the bottom part of the diagram above). Not of all these will be successful, but one cannot doubt the power of such technologies as biometrics. But, so far, they have not delivered a significant change in the performance of Identity.
Identity Paradigms
It is relatively clear that Identity is used widely and is important, that Identity has a complex context, that Identity has performance issues, that the market is underdeveloped, and that many enabling and developing technologies are trying to solve the problem.
But to take the conversation forward, I need to both generalize and conceptualize.
My approach to conceptualizing Identity is the series of paradigms above. Briefly, “knowledge” is simply knowing a secret, “documentation” is having some proof of identity, “technology” is our current malaise, “networking” utilizes the power of current identity hubs and current communications, and “decentralization” is an envisaged future technology-based Identity.
These paradigms do not occur in a strict sequence and they vary by country, industry and organization. But they have evolved over time, so in a sense the world is adding more paradigms as it moves from left to right in the diagram above.
I see most of the planet firmly located in Identity 2 Technology. We have been here a while and we do not seem to be moving anywhere fast. Technology has ‘improved’ but, for the consumer, ease of use is going backwards.
The Challenge
The challenge is ‘what to do next?’. Shall we grin and bear Identity 2? No, that cannot be countenanced in an age of metaverse and web 3 - we must progress. The challenge, as it is generally understood in the Identity world, is how to get from Identity 2 to Identity 3. My position differs – Identity 3 cannot be achieved for a decade or two, so Identity 2.5 is the only way forward! I’ll describe my reasons for such an outlandish statement in my next newsletter.
Regards
Alan