Not a very enticing title I know! As my previous newsletter suggested, Identity is used in many ways in society and there is always an explicit purpose. That is, you do a transaction for a reason. And the reason will likely affect the type of Identity processes required.
So it makes sense to consider Identity as part of the bigger transaction picture and not to simply focus on Identity processes. That is, solving Identity requires a holistic understanding of how Identity is part of transactions. So here is my take on transactions themselves, and specifically Identity-based transactions.
Transactions
Firstly, transactions vary in ‘complexity’. Transactions can be complex - buying a house or opening a bank account. And transactions can be simple - buying an ice cream or buying a newspaper.
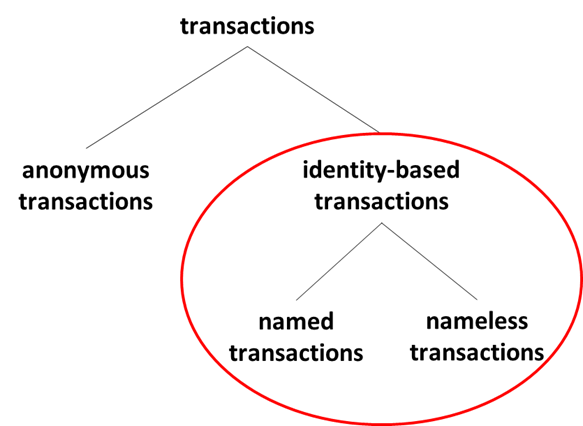
Secondly, there is one primary distinction between anonymous transactions and identity-based transactions:
Anonymous transactions - these could also be called identity-less transactions. This is when you never need to identify or authenticate yourself. Often this is because you pay by cash when purchasing. We have lots of these transactions because we are an open society in which we are not continually monitored. I will not mention anonymous transactions again in these newsletters as they have no relevance for Identity.
Identity-based transactions - identity-processes occur within a transaction for reasons of utility and legal compliance. I term such transactions as identity-based transactions, as the whole basis of the transaction relies on the resolution of identity processes.
Identity-Based Transactions
The above is relatively straightforward, but then comes some subtlety in the two varieties of identity-based transactions.
Named identity-based transactions – these transactions are done ‘in the name of’ a person. Either a person accesses something associated with their name, or a recipient of the transactions learns who the person is. Think of signing onto a banking website and applying for a driving license. In these cases the person wants their personal information to be shared with the recipient.
Nameless identity-based transactions – in these transactions the recipient should never learn who the person is. Think of proving your covid-status or age when entering a bar— the bar should never know who you are.
Some commentators will use the term anonymous to indicate nameless identity-based transactions. This is confusing as these transactions are anonymous with the recipient, but they pertain to a person and require authentication, hence I use the unambiguous term: “nameless identity-based transactions”.
What is important to remember is that both named and nameless identity-based transactions will require a person to be identified and authenticated. It is key to remember that a nameless Identity-based transaction still requires Identity processes of identification and authentication.
Identity Processes
In the above brief discussion of transactions I introduced the two sides of identity processes (I use the term ‘process’ subserviently to the term ‘transaction’).
There are two sides of identity-based processes:
The left-hand side is the ‘proving who you are’ bit, achieved through identifying ourselves and authenticating ourselves. The quality of these steps will, of course, vary, but this is where Identity starts. And rarely, if ever, do we execute an Identity process without a purpose, which is where the right-hand side comes in.
The right-hand side is the ‘what we want to do’ bit, achieved through either Data Use or Data Sharing. Data Use is checking credentials for an authority to act, and Data Sharing is using data for such processes as opening an account. These two themes, of proving who you are and a follow-up action based on data, will run through these newsletters.
These two sides of identity processes are core to identity-based transactions. They are configured in different ways to achieve different transactional objectives.
Looks trivial? It’s not - believe me, there is a lot in the basic concepts above.
Is this definition important?
100% yes:
Firstly, Identity is thoroughly underdeveloped at present (e.g. compared to Payments), so we need clear definitions, and the above is as about as unambiguous as it can be.
Secondly, my definition is focused on the actual steps of identity processes, that is: it is pragmatic. There are no wishy-washy ideological statements here about trust and self-sovereignty - just some concepts that are easily understood and debated.
And thirdly, the structure is a theme that goes through all my work.
In summary
In newsletter one, I established that Identity is important for society. This newsletter, newsletter two, takes the first step in describing some basic terminology to help us discuss Identity. This terminology includes Identity-based transactions (named and nameless) and identity processes (identification and authentication, data use or data sharing). With this established, in the next newsletter, newsletter three - Identity Fundamentals, I describe further refinements of my view of identity processes.
All the best
Alan