10. The Reasonable Future: Identity 2.5
Where I believe the Identity must go.
The title of this newsletter is deliberate – Identity 2.5 is reasonable: that is, there is a coherent argument for Identity 2.5. It is not about ideology nor is it about opinion. Sure, the views expressed are based on my knowledge, but when determining the future of Identity I present a reasoned argument and I ask you to focus on the reasoning for my approach.
A quick recap. I define three current paradigms:
Identity 2 Technology – our current disaster of multiple methods, fraud, and poor customer service
Identity 2.5 Networked – a networked approach that uses current technologies in useful ways
Identity 3 Decentralization – a future where identities exist under the control of the customer.
My Reasoning Summarized
Identity 2 Technology should not be allowed to continue
Identity 3 Decentralized is decades away and we can’t afford to wait for it
Identity 2.5 Networking is demonstratable today and it works.
Given these reasons, Identity 2.5 is our immediate future.
Identity 2 Technology
The status quo is Identity 2 Technology, our current chaotic Identity world. In this paradigm:
we add security through complexity resulting in a horrid customer experience
we cannot support in-person Identity (anyone remember the highly insecure Covid passport?)
on-line fraud is prevalent.
As I have covered the topic in-depth in previous newsletters, I will not go on about these current performance issues here. Suffice to say that we should not accept this state of affairs.
Identity 3 Decentralization
The promised nirvana, Identity 3 Decentralization, cannot be achieved in our current ICT environment, and the industry knows it, even if it will not admit it!
That is quite a statement! There are millions, if not billions, of dollars being invested in decentralization. Fortunes are being made and, if I am right, fortunes will be lost through a failed attempt to implement decentralized Identity (although not necessarily by the same people, unfortunately).
I present three reasons why Decentralization will not deliver an Identity solution now:
Decentralization runs on personal digit devices (PDDs) that are inherently insecure
Decentralization has failed to deliver the intended Decentralized Identifiers (DIDs)
Decentralization has changed focus to Verified Credentials (VCs).
Insecure Personal Digital Devices (PDDs)
Identity 3 Decentralization is based, of course, on not holding central information. In its most fervent forms, it castigates the wicked central masters and exploiters of personal information, and longs for a world where the individual is the sovereign of their own realm. But the data must go somewhere, and that is on personal digital devices.
Now, the first law of ICT security should be “Personal digital devices are inherently insecure”. Decades of viruses, Trojan horses, and fraud surely make this clear. That PC and that smartphone are not highly secure devices. The security of PDDs is average at best.
And we should not be surprised – PDDs are designed to be ‘open’! That is, the movements for open systems, open platforms, and open-source code have delivered great functionality where multiple software components can interact in the same environment. A corollary to this is, of course, that it is much easier for malicious software to be effective. And it is, and so PDDs are insecure.
This means that we will not have a society using secure PDDs for many decades to come. Even if all new PDDs magically became secure, the time it would take to roll over all PDDs is decades. So practically, any Identity solution has to work with a world of insecure PDDs.
See the problem? Pragmatically, Decentralization cannot be secure, and is quite a problem for something that promises a universal solution to Identity! Decentralization has a very large problem of operating within insecure PDDs and it has no solution!
Decentralization has failed to deliver Decentralized Identifiers (DIDs)
DIDs are the fundamental building blocks for Decentralization but the functionality that was envisaged does not exist in practice . W3C has delivered a technical specification of a DID, and no matter what specifications have been published, DIDs have not been delivered.
A good place to start is the W3C Credentials Community Group’s Use Cases for Decentralized Identifiers. One of the example use cases is:
When Sally earned her master’s degree at Oxford, she received a digital diploma which contained a decentralized identifier she provided. Over time, she updates the cryptographic material associated with that DID to use her latest hardware wallet, with biometric protections and a quantum resistant algorithm. A decade after graduation, she applies for a job in Japan, for which she provides her digital diploma by uploading it to the prospective employee’s website. To verify she is the actual recipient of that degree, she uses the decentralized identifier to authenticate, using her current hardware wallet (with rotated keys). In addition to the fact that her name matches the name on the diploma, the cryptographic authentication provides a robust verification of her claim, allowing the employer to rely on Sally’s assertion that she earned a master’s degree from Oxford.
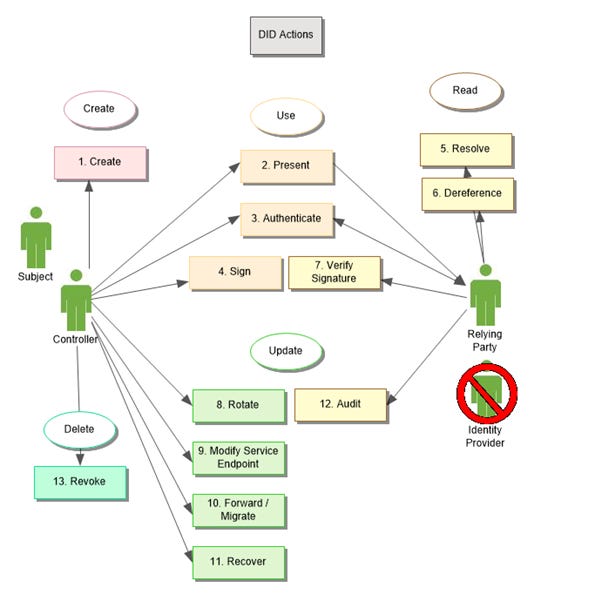
This excerpt clearly shows what was envisaged for DIDs – it replaces a central identity provider with a decentralized identity! This is made explicit in a diagrammatic representation of a DID’s functionality (note the ‘deleted’ Identity Provider on the right):
Looks great, but has anyone seem a prototype yet? The answer is no – all we have is a published specification.
I contend that for Decentralization, DIDs are at the centre of its Identity strategy and it has failed to deliver DIDs because DIDs cannot be delivered in today’s ICT environment.
Decentralization has changed focus to Verified Credentials
Now tech startups are innovators and, when you are stuck, one of the best possible innovations is to change the game. So, now Verified Credentials (VCs) have now been ushered into the limelight. VCs, if implemented correctly, will be secure. But they will not be an Identity solution as they do not do Identification and Authentication. Remember the basic processes of Identity:
VCs sit on the right-hand side – a technique for Data Sharing. The debate about whether they are a good technique has yet to occur, but suffice to say that Data Sharing alone is not an Identity solution. And VCs will likely have other issues which I’ll cover in a future newsletter.
Decentralization, or should I say those commercial entities promoting decentralization, have switched from Identity to managing credentials. They realise that Identity cannot be decentralized in our current environment and so head off to find better pastures!
Decentralized summarized
Decentralization operates on PDDs. PDDs are inherently insecure so Decentralization cannot be secure which is cataclysmic for an Identity solution. This problem is confirmed by Decentralization’s failure to deliver DIDs. The resolution of this issue has been to change focus to Verified Credentials. While VCs have capabilities, they are not general Identity solutions. Decentralization has failed to deliver Identity and has given up the quest to do so.
Identity 2.5 Networked
Why do I believe that Identity 2.5 Networked will work? Well, because it does! Most countries are in Identity 2, whereas the Nordic countries have moved to Identity 2.5.
Now, the standard rejection of that argument is that it only works because the Nordic countries have a national personal number. This is not a good argument. We know that we have perfectly good tokenization techniques that link databases together, so there is no inherent reason that networked solutions are not possible. That networked solutions are easier in Nordic countries is simply an advantage for them.
As the title of my newsletter indicates, I am an advocate for Identity 2.5 Networked. Besides advocacy, I have also created my own solution called General Identity Protocol. I discuss this further in future newsletters.
Summary
Some of the world is hell-bent of achieving Identity 3 Decentralization and, ironically, this is not going to happen anytime soon. With our current proven technologies we have all the building blocks to build sophisticated Identity solutions that provide a good customer experience and good security. That is where we should be spending our time, rather than dreaming of an impossible future.
Regards
Alan